下面文章中有4个段落需要添加小标题,文章需要添加总标题。请从以下选项(A、B、C、 D、E和F)中选出符合意思的标题,并在答题纸上将相应选项的标号涂黑。选项中有一项是多余选项。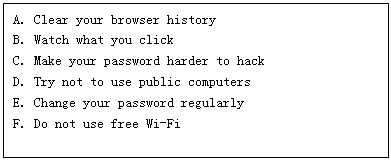
An increase in cyber-attacks and identity theft make the Internet seem like a scary place these days.
Last week, there were reports of a billion dollar theft from European banks and secret viruses on millions of computer systems across Russia, China, India, Iran and elsewhere. This raises a question: How can individuals protect or make it more difficult for hackers to access their information?________________
Hard passwords include upper and lower case letters, numbers and special characters. They should be at least eight characters in length. They should also not spell out words easy for hackers to find, like your pet's name or the name of a family member._______________
A very common mistake made by users is to create one hard password, but then never change it. Remembering a long list of complicated passwords can be difficult. But no password is unbreakable. Hackers are better able hack multiple accounts if those accounts all have the same password. A password management service, like Dashlane or PasswordBox, can help you keep track of hard passwords. These services permit users to easily store and secure their passwords._______________
This goes for all the devices you use in a day–your home computer, your work computer, or your friend's iPad. Internet browsers like Firefox or Chrome keep track of where you've been and what you've done online. They keep records of every site you visited. Information about what you sent from or saved on your computer can be kept for days or weeks. It is very easy for anyone who sees that information to steal a detailed record of your online activities._______________
An increasing number of public places now offer free wireless access to the Internet. Often, a user does not need a password to connect to these wireless networks. These services might be useful, but they're also an easy way for hackers to access everything on your device. Unless you really need it, it is best not to use it.________________
One of the most popular and successful ways hackers infect your computer is through a technique called phishing. Phishing occurs when someone opens an email attachment that looks real. But the attachment is actually a virus that immediately infects the user's computer. If someone sends you a file or a website you did not ask for, it is best to not click on it.








 粤公网安备 44130202000953号
粤公网安备 44130202000953号